Following recent reporting in Germany, Signal has issued a detailed response to clarify the situation and address concerns about its security. The non profit organisation stresses that Signal itself was not hacked, and that encryption, infrastructure, and the integrity of the app’s code was not compromised.
Instead of a technical breach, the incident involved a sophisticated phishing campaign. Attackers posed as “Signal Support” by changing their profile display name and using social engineering techniques to gain trust. Victims were manipulated into sharing sensitive information such as verification codes, which enabled attackers to take over their accounts.
The use of the term “hack” in some reports is therefore misleading, as there was no intrusion into Signal’s technical infrastructure.
How the attack unfolded
Because Signal doesn’t collect user data, much of its understanding of the attacks comes directly from those who were targeted.
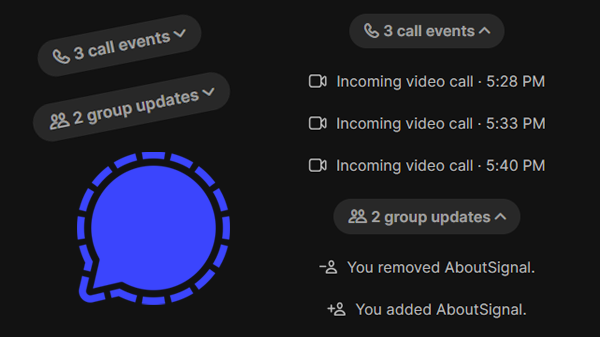
Based on victim reports, Signal describes a clear pattern in how the attacks were carried out. After gaining access to login credentials, attackers would take control of the account and often change the linked phone number. Victims were told that being logged out was expected behavior and were encouraged to “re-register.” Believing they were restoring access, they unknowingly created new accounts while their original ones remained compromised. As a result, many didn’t notice the takeover, allowing attackers to use hijacked accounts to contact people in their networks.
New changes to help hinder attacks
Signal acknowledges that phishing and social engineering affect all major messaging platforms. However, the organisation notes that the consequences are particularly serious given the high level of trust users place in its service.
The incidents highlight a broader reality in cybersecurity: even strong technical defenses can’t prevent attackers from exploiting human behavior.
In response, Signal says it will roll out new measures in the coming weeks to help prevent and detect phishing attempts. Specific details have not yet been disclosed.
Stay alert
Signal urges users to remain cautious and aware of potential scams. It reiterates that Signal Support will never ask for verification codes or PINs through messages. Users are also encouraged to enable Registration Lock (Settings > Account > Registration Lock) to add an extra layer of protection.
For those who want more information about how attackers work and how to protect yourself on Signal, read our article: Tentativi di phishing su Signal – come funzionano e come proteggersi.
Signal’s full response can be read on social media Bluesky, Mastodon e X.
A response to recent reporting in Germany, in service of clarity and accountability: First, it’s important to be precise when it comes to critical infrastructure like Signal. Signal was not “hacked” — in that our encryption, infrastructure, & the integrity of the app’s code was not compromised. 1/
— Signal (@signal.org) 27 april 2026 om 22:53
Resta informato
Vuoi rimanere aggiornato sulle ultime novità Signal notizie, suggerimenti e aggiornamenti? Seguici su Threads, Bluesky o Mastodon.